Mobile Trusted Module Wikipedia
These modules traditionally come in the form of a plug-in card or an external device that attaches directly to a computer or network server. The absence of trusted hardware prevents mobile devices from adopting the recent security features.

Compare Millions Of Mobile Prices From The Most Trusted Stores Telefonos Celulares Celulares Antiguos Gadgets Tecnologicos
Unfortunately the MTM speci-fication has lacked broad industry support and has never been widely adopted in practice in spite of the much ef-forts by TCG.

Mobile trusted module wikipedia. The TEE optionally offers a trusted user interface which can be used to construct user authentication on a mobile device. Trusted Platform Module TPM By. Intel TXT uses a Trusted Platform Module TPM and cryptographic techniques to provide measurements of software and platform components so that system software as well as local and remote management applications may use those measurements to make trust decisions.
The source repository for the Trusted Platform Module TPM20 tools based on tpm2-softwaretpm2-tss. Trusted Platform Module TPM is an international standard for a secure cryptoprocessor which is a dedicated microprocessor designed to secure hardware by integrating cryptographic keys into devices. This is particularly important as the Internet of Things IoT proliferates because to avoid being hacked.
TCGs most successful effort was the development of a Trusted Platform Module TPM a semiconductor intellectual property core or integrated circuit that conforms to the specification to enable trusted computing features in computers and mobile devices. They are the concrete implementation of the flow logic of the authentication and several login modules can be combined to make a login module authentication stack in this regard are the ClientCertLoginModule and the CertPersisterLoginModule. TPM Trusted Platform Module is a computer chip microcontroller that can securely store artifacts used to authenticate the platform your PC or laptop.
Because this module is for all intents and purposes inaccessible outside the computer ecosystem that ecosystem can trust the keys and other cryptographic information it receives from the root of trust module to be authentic and authorized. A hardware security module HSM is a physical computing device that safeguards and manages digital keys performs encryption and decryption functions for digital signatures strong authentication and other cryptographic functions. Вміст доступний на умовах cc by-sa 30 якщо не вказано інше.
A Trusted Platform Module TPM is a specialized chip on an endpoint device that stores RSA encryption keys specific to the host system for hardware authentication. The Trusted Platform Module TPM is an implementation of a secure cryptoprocessor that brings the notion of trusted computing to ordinary PCs by enabling a secure environment. Download Wikipedia for Android or iOS Save your favorite articles to read offline sync your reading lists across devices and customize your reading experience with the official Wikipedia app.
It defines the Protected Environment itself and includes discussion of modern mobile device architecture Roots of Trust and. The SAP login modules which are the implementation of Java Authentication and Authorization Service in SAP NetWeaver AS Java. Trusted Computing Group Administration 3855 SW 153rd Drive Beaverton Oregon 97003.
Each TPM chip contains an RSA key pair called the Endorsement Key EK. In practice a TPM can be used for various different security applications such as. Ously proposed a new standard called Mobile Trusted Module MTM 42.
Readthedocs for information on installation man-pages and more. The TPM 20 Mobile Reference Architecture Specification defines architecture for the implementation of a TPM 20 with protected capabilities and secure storage executing within a Protected Environment in a mobile platform. Citation needed Present TPM implementations focus on providing a tamper-proof boot environment and persistent and volatile storage encryption.
Authentication edit The TEE is well-suited for supporting biometric ID methods facial recognition fingerprint sensor and voice authorization which may be easier to use and harder to steal than PINs and passwords.

Jd Edwards Procurement Module Jd Edwards Procurement Procurement Management

Pin By Michel Rochette On Technology Photo Album Navigation Vertical

Pdf Generic Secure And Modular Gsm Methodology For Design And Implementation Of Secure Mobile Applications
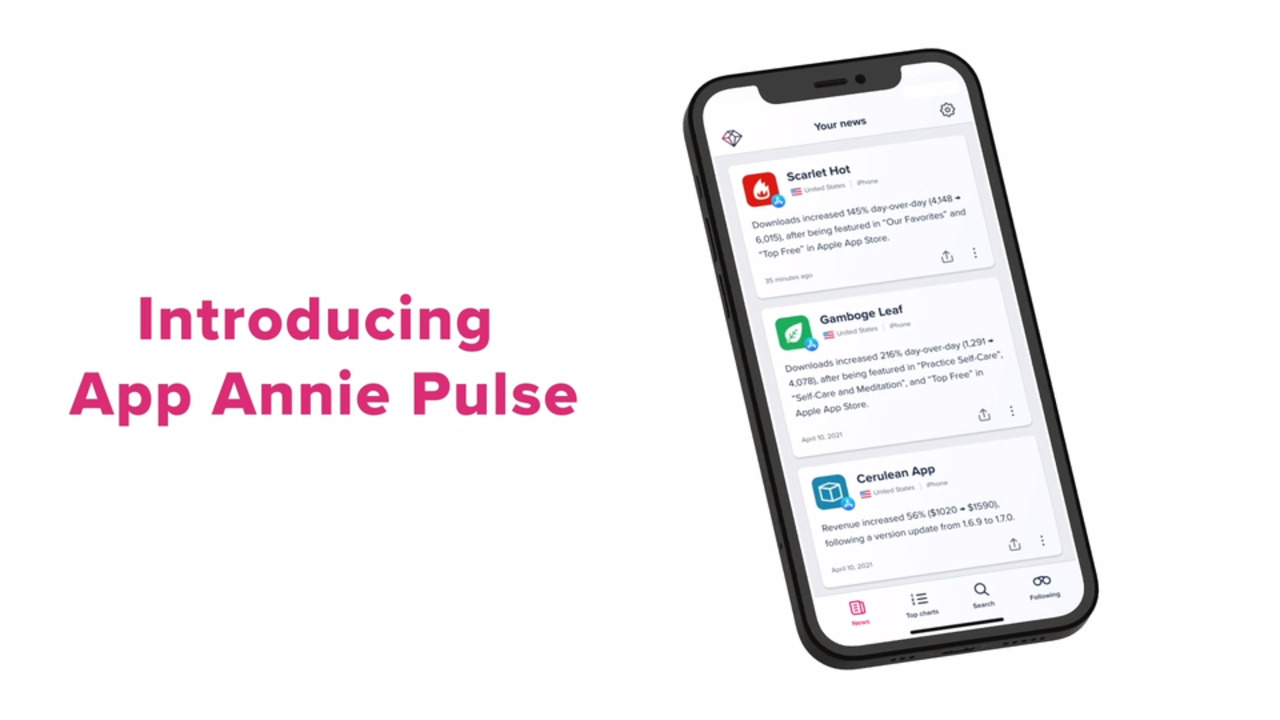
App Annie The App Analytics And App Data Industry Standard

Mobile First Customer Service Platform Helpshift

Samsung Akan Gelar Galaxy Unpacked Pertama 2021 Hadirkan Galaxy S21 Di 2021 Samsung Galaxy Samsung Perlengkapan Kamera

17 Remote Car Starter Installation Wiring Diagram Car Diagram Wiringg Net Car Alarm Home Security Systems Alarm System

Install Openkm Document Management System In Ubuntu Document Management System Management Knowledge Management

Violations Of Dry Are Typically Referred To As Wet Solutions Which Is Commonly Taken To Stand For Either Write Everything Twice We E Solutions Wet Writing

Super Smallest Wireless Ip Wifi Network Internet Micro Hidden Spy Camera Dvr Cons Home Security Systems Wireless Home Security Systems Wireless Home Security

Diagram Illustrating How Different Screen Sizes And Resolutions Relate To One Another Nexus One First Iphone Google Nexus

Ssds Raid 0 Degradation 12 Days Sf 2281 Writing Chart Directions

Powerpuff Girls Yu Gi Oh Awesome Yugioh Chibi Powerpuff
Https Ec Europa Eu Cefdigital Wiki Download Attachments 306775200 Dss 20webinar 20q4 202020 20v1 00 Pdf Version 2 Modificationdate 1608218698692 Api V2

Visual Studio 2012 To Compile Mozilla S Firefox Project Visual Studio Firefox

Hewlett Packard Phone Malaysia Ads Print Hewlett Packard Laptop Computers Ink Toner



0 Response to "Mobile Trusted Module Wikipedia"
Post a Comment